The High Cost of a 'Check-the-Box' Mentality
Getting a cyber insurance policy used to be as simple as filling out a basic questionnaire and paying a premium. Those days are dead. After a wave of massive ransomware attacks and systemic failures in cloud infrastructure, insurers have shifted from being passive payers to aggressive auditors. If you try to buy a policy today without the right security controls in place, you'll either face a premium that looks like a phone number or, more likely, a flat-out denial of coverage.
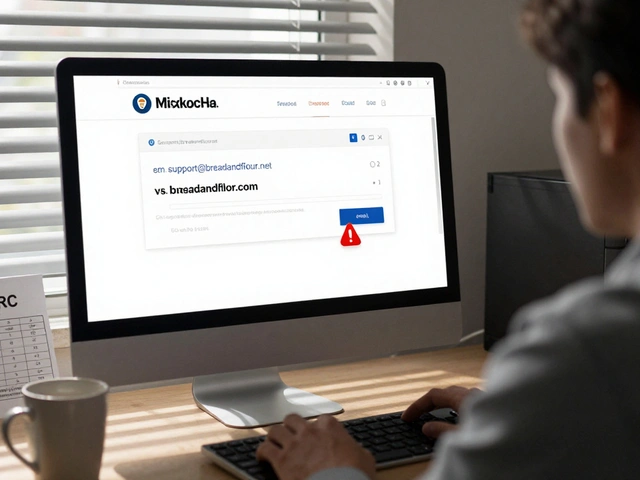
The problem is that many businesses treat cyber insurance requirements like a chore rather than a strategy. They implement a tool just to pass the application, then turn it off or ignore the alerts. Insurers are catching on. They now demand proof of operational effectiveness, not just a 'yes' on a form. If you have a breach and the insurer finds you lied about your security posture-even by accident-they can deny your claim entirely, leaving you to foot a multi-million dollar recovery bill alone.
Quick Summary: Must-Have Controls for 2026
- MFA Everywhere: No exceptions for admins or legacy systems.
- EDR/XDR Deployment: Basic antivirus isn't enough; you need behavioral detection.
- Backup Integrity: Immutable, off-site backups that are tested monthly.
- Patch Management: A documented system for critical updates within 72 hours.
- Privileged Access: Strict limits on who can touch the "crown jewels" of your data.
The Non-Negotiable Gatekeepers: MFA and Access Control
If you don't have Multi-Factor Authentication (MFA) a security system that requires more than one method of authentication to verify a user's identity enabled on every single external-facing entry point, you are essentially uninsurable. Insurers have seen too many accounts compromised via simple password spraying or credential stuffing. They aren't just talking about your email anymore; they want to see MFA on VPNs, RDP ports, and cloud consoles.
But here is the catch: SMS-based codes are increasingly seen as weak. To get the best rates, you should move toward phishing-resistant MFA, such as FIDO2 a set of standards for creating a more secure and simpler way to authenticate users to online services keys or biometric authentication. When an underwriter asks about access, they want to know if you're using the principle of least privilege. This means a marketing intern shouldn't have administrative access to the server where your customer credit card data lives.
Moving Beyond Antivirus with EDR and XDR
Traditional antivirus software looks for known "signatures"-basically a digital fingerprint of a virus. But modern threats are "fileless" or use polymorphic code that changes its shape to avoid detection. This is why Endpoint Detection and Response (EDR) a technology that continuously monitors endpoints to detect and respond to cyber threats is now a mandatory requirement for mid-to-large enterprises.
EDR doesn't just block a file; it watches behavior. If a user account suddenly starts encrypting thousands of files in the background, EDR flags that as ransomware behavior and kills the process. Many insurers now push for Extended Detection and Response (XDR) an evolution of EDR that integrates data from endpoints, networks, and cloud workloads for a holistic view of security, because it connects the dots across the entire network. For example, it can see a suspicious login from a foreign country followed by an unusual data export to a Dropbox account, treating them as one single incident rather than two separate events.

The Backup Paradox: Availability vs. Integrity
Everyone has backups, but very few have backups that actually work during a ransomware crisis. Attackers now spend weeks inside a network specifically looking for the backup server so they can delete or encrypt the archives before triggering the main attack. If your backups are connected to the same domain as your primary data, they are just as vulnerable.
Insurers now require "immutable backups." An Immutable Backup a backup that cannot be changed, deleted, or overwritten for a specific period ensures that once data is written, it stays that way. Whether you use a write-once-read-many (WORM) drive or a locked cloud bucket, the goal is to create a gap the attacker can't bridge. You should also be running a "recovery drill" at least once a quarter. If it takes you three weeks to restore a single server, your business might be dead before the data is back.
Vulnerability Management and the Patching Race
Zero-day vulnerabilities are the holy grail for hackers. When a critical flaw in a common tool like Microsoft Exchange an enterprise-grade mail and calendar server is announced, the race begins. Attackers start scanning the internet for unpatched servers within hours. If your company takes a month to patch critical vulnerabilities, you are a high-risk asset.
Your insurance application will likely ask for your "patching cadence." You need a documented process that proves you prioritize critical patches. A good rule of thumb is the 72-hour window: critical security updates should be tested and deployed within three days of release. Using a Vulnerability Scanner a tool that identifies security weaknesses in a network or application like Nessus or Qualys helps you find these holes before the insurance auditor does.
Comparing Control Levels for Different Policy Tiers
| Control Area | Basic Coverage (Small Biz) | Enterprise Coverage (High Risk) | Impact on Premium |
|---|---|---|---|
| MFA | Required for Admin/Email | Required for ALL Users | High Reduction |
| Endpoint Security | Standard Antivirus | Managed EDR/XDR (24/7 SOC) | Medium Reduction |
| Backups | Daily Cloud Backups | Air-gapped / Immutable | High Reduction |
| Patching | Monthly Cycle | Criticals within 72 Hours | Medium Reduction |
| Network | Single Firewall | Micro-segmentation / Zero Trust | Low-Medium Reduction |

The Human Element: Training and Governance
You can spend millions on the best tools, but if an employee clicks a "Urgent: Invoice Overdue" link in a fake email, your defenses can be bypassed. Insurers now look for evidence of a Security Awareness Training educational programs designed to reduce human risk in cybersecurity program. They don't just want to know if you have a training video; they want to see your phishing simulation results. If 40% of your staff is clicking on fake links, your risk profile goes up.
Beyond training, governance is key. Do you have an Incident Response Plan (IRP)? This is a literal playbook that tells your team exactly who to call and what to do the moment a breach is detected. An IRP prevents the panic-driven mistakes-like accidentally deleting evidence or paying a ransom without a negotiation strategy-that can lead to higher losses and denied claims.
Common Pitfalls That Lead to Denied Claims
The most dangerous phrase in a cyber insurance application is "to the best of my knowledge." If you claim you have MFA enabled on all accounts, but your old legacy server for the accounting department is still using a password from 2012, you've created a gap in your coverage. If that legacy server is the entry point for a breach, the insurer may argue that you misrepresented your security posture.
Another common mistake is ignoring "shadow IT." This happens when a department buys a SaaS tool with a corporate credit card without telling the IT team. If that tool has a security flaw and leaks your data, you might find that your policy doesn't cover assets that weren't documented in your risk assessment. Your inventory needs to be comprehensive; you can't protect what you don't know exists.
Does having cyber insurance mean I'm secure?
Absolutely not. Insurance is a financial risk transfer tool, not a security tool. It helps you recover the money lost after a disaster, but it won't stop the disaster from happening. Think of it like fire insurance: it pays to rebuild the house, but it doesn't stop you from leaving the stove on.
What happens if I can't meet all the requirements?
You can still get coverage, but it will be more expensive and likely come with higher deductibles. Some insurers may offer a "remediation period" where they give you 30-90 days to implement a specific control (like EDR) before the policy is canceled or premiums are hiked.
Is MFA really that important for insurance?
Yes. Statistically, a huge percentage of breaches start with compromised credentials. Insurers view a lack of MFA as an open door. In most current markets, MFA on critical systems is a binary requirement: you either have it, or you don't get a policy.
How often should I review my security controls?
At a minimum, review them annually before your policy renewal. However, since the threat landscape changes weekly, you should be performing vulnerability scans monthly and reviewing access logs and backup integrity weekly.
What is a 'Zero Trust' architecture in the eyes of an insurer?
Zero Trust is the idea that no user or device is trusted by default, even if they are inside the corporate network. For an insurer, this means you've moved away from a "castle and moat" security model and instead verify every single request for data, regardless of where it comes from.
Next Steps for Business Owners
If you're preparing for a renewal or shopping for a new policy, start by performing a gap analysis. Don't guess-run a report on your MFA adoption and check your last three backup restore attempts. If you find gaps, prioritize them based on the "Must-Have" list provided above. Focus on MFA first, then immutable backups, then EDR. Getting these three right will do more to lower your premiums and protect your business than any other combination of tools.